- Call for Papers
- Key Dates

- First submission deadline: 20 June, 2012
- Submission deadline: 20 August, 2012 (extended)
- Notification: 20 October, 2012
Revision deadline: 30 November, 2012 - Final decision and notification: 20 January, 2013
- Subject Coverage
- Trends in new threat and vulnerability identification
- Data mining and web mining for risk assessment
- Models and visualisation tools for behaviour understanding
- Gest
Editors contact information:
babiga.birregah[at]utt.fr
iting[at]nuk.edu.tw
RAMSM 2012
Special Issue in
International Journal of Web Engineering and Technology (IJWET-
Inerscience)
You are here
International Journal of Web Engineering and
Technology (IJWET)
|
Call for Papers Special Issue on: "Risk Assessment in Mobile Social Media: Trends, Threats, Vulnerabilities and Countermeasures" |
 |
Guest Editors:
Dr. Babiga Birregah, University of Technology of Troyes, France
Dr. I-Hsien Ting, National University of Kaohsiung, Taiwan
In recent years the world has been experiencing the exponential growth of mobile social media and networks and their related platforms. The proliferation of innovative mobile network applications and services leads to the emergence of new forms of threats for users, organisations (enterprises, communities, developers, etc.) and society.
Social media have become a large platform for illegal activities such as malware propagation, identity theft, child pornography, etc. It is therefore a major objective to detect abnormal behaviours and to have efficient tools to assess these new forms of threats.
This special issue aims to present the state-of-the-art in risk assessment in mobile social media and networks. Authors are encouraged to submit their research papers on latest trends, threats, vulnerabilities and countermeasures.
Suitable topics include but are not limited to:
- Trends in new threat and vulnerability identification
- Survey of risk assessment in mobile social media
- Empirical and comparative studies (microblogging, social networks, online professional networks, etc.)
- Security and privacy issues in mobile social media (digital confidence, privacy policy integration in mobile application)
- Digital identity theft
- Trust and reputation
- Mobile social media use among teens and young adults: trends and vulnerabilities
- Best practices and applications in mobile social media
- Competitive intelligence (brand attack, social media crisis, rumours, etc.)
- Societal and political issues (e-citizenship, e-government, etc.)
- Mobile cloud computing
- Data mining and web mining for risk assessment
- Data collection and new tools for data analysis (semantic approaches, data mining, etc.)
- Data pre-processing for data from mobile social media
- Methods and tools for identification and assessment of new forms of threats
- Risk assessment in mobile social network services: URL-shortening, geolocation, etc.
- Convergence mobile phone, social media and network
- Anomaly detection
- Mobile network forensics: indicators, metrics, etc.
- Models and visualisation tools for behaviour understanding
- User modelling and pattern identification in mobile social media
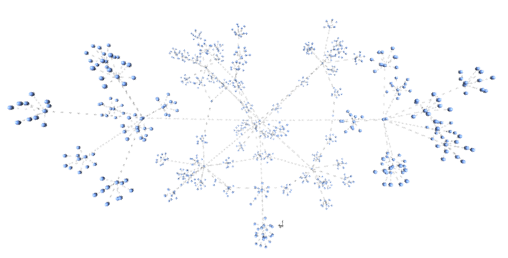
- Visualisation tools and techniques for cybercrime analysis
- Mathematical models: fuzzy logic, Bayesian approaches, probabilistic and statistical methods, kernel methods, etc.
Submitted papers should not have been previously published nor be currently under consideration for publication elsewhere. (N.B. Conference papers may only be submitted if the paper was not originally copyrighted and if it has been completely re-written).
All papers are refereed through a peer review process. A guide for authors, sample copies and other relevant information for submitting papers are available on the Author Guidelines page.
First submission deadline: 20 June, 2012
First notification: 20 August, 2012
Revision deadline: 30 September, 2012
Final decision and notification: 20 November, 2012
All papers must be submitted online. To submit a paper, please go to Online Submissions of Papers. If you experience any problems submitting your paper online, please contact submissions@inderscience.com, describing the exact problem you experience. (Please include in your email the title of the Special Issue, the title of the Journal and the names of the Guest Editors)

